K8S配置管理
- Kubernetes
- 2024-08-15
- 7715热度
- 10评论
K8S-配置管理
ConfigMap
ConfigMap 是 Kubernetes 中的一个核心资源对象,用于存储非机密性的配置数据,如键值对、配置文件等。它允许开发者将应用程序的配置与容器化的应用程序分开管理,从而实现配置的灵活和动态管理。ConfigMap 的数据可以通过环境变量、命令行参数或作为卷挂载到 Pod 中,以此来供应用程序使用。这种分离配置和代码的做法提高了应用程序的可移植性和可维护性。
创建ConfigMap资源的方式如下:
[root@master-01 ~]# vim /k8spod/config/configmap.yaml
apiVersion: v1
kind: ConfigMap
metadata:
name: game-demo
data:
player_initial_lives: "3"
ui_properties_file_name: "user-interface.properties"
game.properties: |
enemy.types=aliens,monsters
player.maximum-lives=5
user-interface.properties: |
color.good=purple
color.bad=yellow
allow.textmode=true创建资源并查看资源创建情况
[root@master-01 ~]# kubectl create -f /k8spod/config/configmap.yaml
configmap/game-demo created[root@master-01 ~]# kubectl get configmap
NAME DATA AGE
game-demo 4 109s
kube-root-ca.crt 1 69d[root@master-01 ~]# kubectl describe configmap game-demo
Name: game-demo
Namespace: default
Labels: <none>
Annotations: <none>
Data
====
game.properties:
----
enemy.types=aliens,monsters
player.maximum-lives=5
player_initial_lives:
----
3
ui_properties_file_name:
----
user-interface.properties
user-interface.properties:
----
color.good=purple
color.bad=yellow
allow.textmode=true
BinaryData
====
Events: <none>通过Pod引用ConfigMap或将ConfigMap里面的值配置为环境变量(读者可以先看下面的例子,此处放到最后看)
apiVersion: v1
kind: Pod
metadata:
name: configmap-demo-pod
spec:
containers:
- name: demo
image: alpine
command: ["sleep", "3600"]
env:
- name: PLAYER_INITIAL_LIVES
valueFrom:
configMapKeyRef:
name: game-demo
key: player_initial_lives
- name: UI_PROPERTIES_FILE_NAME
valueFrom:
configMapKeyRef:
name: game-demo
key: ui_properties_file_name
volumeMounts:
- name: config
mountPath: "/config"
readOnly: true
volumes:
- name: config
configMap:
name: game-demo
items:
- key: "game.properties"
path: "game.properties"
- key: "user-interface.properties"
path: "user-interface.properties"创建资源并查看资源创建情况
[root@master-01 ~]# kubectl create -f /k8spod/config/configmap-pod.yaml
pod/configmap-demo-pod created
[root@master-01 ~]# kubectl get pods
NAME READY STATUS RESTARTS AGE
cluster-test-665f554bcc-bcw5v 1/1 Running 117 (53m ago) 53d
configmap-demo-pod 1/1 Running 0 46s登录到容器内,查看环境变量和文件是否正常挂载
[root@master-01 ~]# kubectl exec -it configmap-demo-pod -- env | grep PLAYER
PLAYER_INITIAL_LIVES=3
[root@master-01 ~]# kubectl exec -it configmap-demo-pod -- env | grep UI
UI_PROPERTIES_FILE_NAME=user-interface.properties
[root@master-01 ~]# kubectl exec -it configmap-demo-pod -- ls /config
game.properties user-interface.properties
[root@master-01 ~]# kubectl exec -it configmap-demo-pod -- cat /config/game.properties
enemy.types=aliens,monsters
player.maximum-lives=5
[root@master-01 ~]# kubectl exec -it configmap-demo-pod -- cat /config/user-interface.properties
color.good=purple
color.bad=yellow
allow.textmode=true在宿主机下创建目录及准备挂载的文件
[root@master-01 ~]# mkdir /conf
[root@master-01 ~]# vim /conf/nginx.conf
user nginx;
worker_processes auto;
worker_cpu_affinity 00000001 00000010 00000100 00001000;
error_log /var/log/nginx/error.log warn;
pid /var/run/nginx.pid;
worker_rlimit_nofile 65536;
events {
worker_connections 65535;
accept_mutex on;
multi_accept on;
}
[root@master-01 ~]# vim /conf/coremail.conf
mysql=127.0.0.1
username=caijxlinux
passwd=123通过命令将所需目录下的文件批量配置为ConfigMap
[root@master-01 ~]# kubectl create cm cmfromdir --from-file=/conf/
configmap/cmfromdir created查看资源的创建情况,可以观察到创建的内容与文件的内容一致
[root@master-01 ~]# kubectl get cm
NAME DATA AGE
cmfromdir 2 39s
kube-root-ca.crt 1 69d[root@master-01 ~]# kubectl describe cm cmfromdir
Name: cmfromdir
Namespace: default
Labels: <none>
Annotations: <none>
Data
====
coremail.conf:
----
mysql=127.0.0.1
username=caijxlinux
passwd=123
nginx.conf:
----
user nginx;
worker_processes auto;
worker_cpu_affinity 00000001 00000010 00000100 00001000;
error_log /var/log/nginx/error.log warn;
pid /var/run/nginx.pid;
worker_rlimit_nofile 65536;
events {
worker_connections 65535;
accept_mutex on;
multi_accept on;
}
BinaryData
====
Events: <none>将所需目录下的文单个文件配置为ConfigMap
[root@master-01 ~]# kubectl create cm cmfromfile --from-file=/conf/coremail.conf
configmap/cmfromfile created修改所需配置文件的文件名为coremail-conf,资源创建完成后,可以观察到文件的名称从coremail.conf修改为coremail-conf
[root@master-01 ~]# kubectl create cm cmspecialname --from-file=coremail-conf=/conf/coremail.conf
configmap/cmspecialname created
[root@master-01 ~]# kubectl describe cm cmspecialname
Name: cmspecialname
Namespace: default
Labels: <none>
Annotations: <none>
Data
====
coremail-conf:
----
mysql=127.0.0.1
username=caijxlinux
passwd=123
BinaryData
====
Events: <none>通过宿主机的文件生成环境变量(ConfigMap)
[root@master-01 ~]# kubectl create cm cmenv --from-env-file=/conf/coremail.conf
configmap/cmenv created在环境变量较少的情况下,使用--from-literal参数生成环境变量
[root@master-01 ~]# kubectl create cm cmenvliteral --from-literal=LEVAL=INFO --from-literal=ENCRYPT=MD5
configmap/cmenvliteral created
[root@master-01 ~]# kubectl describe cm cmenvliteral
Name: cmenvliteral
Namespace: default
Labels: <none>
Annotations: <none>
Data
====
ENCRYPT:
----
MD5
LEVAL:
----
INFO
BinaryData
====
Events: <none>通过envFrom字段,将文件内容全部注入到Pod内的环境变量,并为注入的环境变量添加前缀,区分是从哪个configMap内生成的
[root@master-01 ~]# kubectl create deployment dp-cm --image=registry.cn-guangzhou.aliyuncs.com/caijxlinux/nginx:v1.15.1 --dry-run=client -oyaml > /k8spod/config/envfrom.yaml
[root@master-01 ~]# vim /k8spod/config/envfrom.yaml
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
app: dp-cm
name: dp-cm
spec:
replicas: 1
selector:
matchLabels:
app: dp-cm
strategy: {}
template:
metadata:
labels:
app: dp-cm
spec:
containers:
- image: registry.cn-guangzhou.aliyuncs.com/caijxlinux/nginx:v1.15.1
name: nginx
envFrom:
- configMapRef:
name: cmenv
prefix: CJX创建资源并查看容器内的环境变量
[root@master-01 ~]# kubectl create -f /k8spod/config/envfrom.yaml deployment.apps/dp-cm created
[root@master-01 ~]# kubectl get pods
NAME READY STATUS RESTARTS AGE
cluster-test-665f554bcc-bcw5v 1/1 Running 158 (51m ago) 55d
dp-cm-75cd98497c-s9g7m 1/1 Running 0 15s
[root@master-01 ~]# kubectl exec -it dp-cm-75cd98497c-s9g7m -- env | grep CJX
CJXmysql=127.0.0.1
CJXpasswd=123
CJXusername=caijxlinux以文件的形式将ConfigMap挂载到容器内部
[root@master-01 ~]# cat /k8spod/config/fielmount.yaml
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
app: dp-cm
name: dp-cm
spec:
replicas: 1
selector:
matchLabels:
app: dp-cm
strategy: {}
template:
metadata:
labels:
app: dp-cm
spec:
volumes:
- name: filemount
configMap:
name: cmfromfile
containers:
- image: registry.cn-guangzhou.aliyuncs.com/caijxlinux/nginx:v1.15.1
name: nginx
volumeMounts:
- name: filemount
mountPath: /mnt/cmfile创建资源,查看ConfigMap是否以文件的形式挂载到容器内部
[root@master-01 ~]# kubectl create -f /k8spod/config/fielmount.yaml
deployment.apps/dp-cm created
[root@master-01 ~]# kubectl get pods
NAME READY STATUS RESTARTS AGE
cluster-test-665f554bcc-bcw5v 1/1 Running 159 (10m ago) 55d
dp-cm-8676d97cd9-cg5hl 1/1 Running 0 2m36s
[root@master-01 ~]# kubectl exec -it dp-cm-8676d97cd9-cg5hl -- cat /mnt/cmfile/coremail.conf
mysql=127.0.0.1
username=caijxlinux
passwd=123自定义挂载的ConfigMap文件名
[root@master-01 ~]# vim /k8spod/config/rename.yaml
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
app: dp-cm
name: dp-cm
spec:
replicas: 1
selector:
matchLabels:
app: dp-cm
strategy: {}
template:
metadata:
labels:
app: dp-cm
spec:
volumes:
- name: filemount
configMap:
name: cmfromfile
items:
- key: coremail.conf
path: coremail.cf
containers:
- image: registry.cn-guangzhou.aliyuncs.com/caijxlinux/nginx:v1.15.1
name: nginx
volumeMounts:
- name: filemount
mountPath: /mnt/cmfile创建资源,观察到ConfigMap已被重命名
[root@master-01 ~]# kubectl create -f /k8spod/config/rename.yaml
deployment.apps/dp-cm created
[root@master-01 ~]# kubectl get pods
NAME READY STATUS RESTARTS AGE
cluster-test-665f554bcc-bcw5v 1/1 Running 159 (22m ago) 55d
dp-cm-856799758d-xwqs4 1/1 Running 0 4s
[root@master-01 ~]# kubectl exec -it dp-cm-856799758d-xwqs4 -- ls /mnt/cmfile
coremail.cf自定义挂载ConfigMap文件的权限,设置默认权限或者针对某个文件单独设置权限
[root@master-01 ~]# vim /k8spod/config/permission.yaml
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
app: dp-cm
name: dp-cm
spec:
replicas: 1
selector:
matchLabels:
app: dp-cm
strategy: {}
template:
metadata:
labels:
app: dp-cm
spec:
volumes:
- name: filemount
configMap:
name: cmfromfile
items:
- key: coremail.conf
path: coremail.cf
mode: 0777
defaultMode: 0666
- name: filemount-2
configMap:
name: game-demo
items:
- key: user-interface.properties
path: user-interface.conf
defaultMode: 0666
containers:
- image: registry.cn-guangzhou.aliyuncs.com/caijxlinux/nginx:v1.15.1
name: nginx
volumeMounts:
- name: filemount
mountPath: /cmfile
- name: filemount-2
mountPath: /cm创建资源并查看ConfigMap挂载情况,在本例中,filemount配置了两个权限,但是mode权限优先级会更高,所以挂载的文件权限应该为0777,而filemount-2中,只有defaultMode,所以挂载的文件权限为0666。由于在容器内部文件是通过符号链接进行更新,所以可以根据箭头的指向找到原始文件
[root@master-01 ~]# kubectl create -f /k8spod/config/permission.yaml
deployment.apps/dp-cm created
[root@master-01 ~]# kubectl get pods
NAME READY STATUS RESTARTS AGE
cluster-test-665f554bcc-bcw5v 1/1 Running 160 (3m4s ago) 55d
dp-cm-6f99d69d5b-58cc8 1/1 Running 0 5s[root@master-01 ~]# kubectl exec -it dp-cm-6f99d69d5b-58cc8 -- ls -l /cmfile
total 0
lrwxrwxrwx 1 root root 18 Aug 6 20:47 coremail.cf -> ..data/coremail.cf
[root@master-01 ~]# kubectl exec -it dp-cm-6f99d69d5b-58cc8 -- ls -l /cmfile/..data
lrwxrwxrwx 1 root root 32 Aug 6 20:47 /cmfile/..data -> ..2024_08_06_20_47_28.2294513666
[root@master-01 ~]# kubectl exec -it dp-cm-6f99d69d5b-58cc8 -- ls -l /cmfile/..2024_08_06_20_47_28.2294513666
total 4
-rwxrwxrwx 1 root root 47 Aug 6 20:47 coremail.cf[root@master-01 ~]# kubectl exec -it dp-cm-6f99d69d5b-58cc8 -- ls -l /cm
total 0
lrwxrwxrwx 1 root root 26 Aug 6 20:47 user-interface.conf -> ..data/user-interface.conf
[root@master-01 ~]# kubectl exec -it dp-cm-6f99d69d5b-58cc8 -- ls -l /cm/..data
lrwxrwxrwx 1 root root 32 Aug 6 20:47 /cm/..data -> ..2024_08_06_20_47_28.2930645464
[root@master-01 ~]# kubectl exec -it dp-cm-6f99d69d5b-58cc8 -- ls -l /cm/..2024_08_06_20_47_28.2930645464
total 4
-rw-rw-rw- 1 root root 59 Aug 6 20:47 user-interface.confSecret
Kubernetes Secret 是一种用于存储和管理敏感数据的机制,如密码、OAuth 令牌和 SSH 密钥。这些数据以加密的形式存储在 API 服务器的底层数据存储(etcd)中,以减少敏感信息在集群中的暴露风险。Secret 可以通过多种方式在 Pod 中使用,包括作为环境变量、卷挂载或配置文件,从而允许应用程序安全地访问这些敏感信息,而无需将这些信息硬编码在配置文件或镜像中。
| 类型 | 场景 |
|---|---|
| Opaque | 通用型Secret,默认类型 |
| service-account-token | 作用于ServiceAccount,包含一个令牌,用于标识API服务账户 |
| dockerconfigjson | 下载私有仓库镜像使用的Secret,和宿主机的/root/.docker/config.json一致,宿主机登录后即可产生该文件 |
| basic-auth | 用于使用基本认证(账号密码)的Secret,可以使用Opaque取代 |
| ssh-auth | 用于存储ssh密钥的Secret |
| tls | 用于存储HTTPS域名证书文件的Secret,可以被Ingress使用 |
| bootstrap.kubernetes.io/token | 一种简单的 bearer token,用于创建新集群或将新节点添加到现有集群,在集群安装时可用于自动颁发集群的证书 |
将登录账户和密码写入文件,通过文件创建Secret
[root@master-01 ~]# echo -n 'admin' > ./username.txt
[root@master-01 ~]# echo -n 'S!B\*d$zDsb=' > ./password.txt
[root@master-01 ~]# kubectl create secret generic db-user-pass --from-file=username=./username.txt --from-file=password=./password.txt
secret/db-user-pass created查看资源创建情况,可以观察到内容被加密,可使用bash64的方法进行解密
[root@master-01 ~]# kubectl get secrets
NAME TYPE DATA AGE
db-user-pass Opaque 2 30s
[root@master-01 ~]# kubectl get secrets -oyaml
apiVersion: v1
items:
- apiVersion: v1
data:
password: UyFCXCpkJHpEc2I9
username: YWRtaW4=
kind: Secret
metadata:
creationTimestamp: "2024-08-12T20:49:54Z"
name: db-user-pass
namespace: default
resourceVersion: "1773949"
uid: 83e8f74d-3e69-4e6d-979b-69e72d00b28a
type: Opaque
kind: List
metadata:
resourceVersion: ""[root@master-01 ~]# echo "UyFCXCpkJHpEc2I9" | base64 -d
S!B\*d$zDsb=通过--from-literal参数创建,注意:有特殊符号时需要进行转义或者使用单引号
[root@master-01 ~]# kubectl create secret generic dev-db-secret --from-literal=username=devuser --from-literal=password=123
secret/dev-db-secret createdsecret拉取私有镜像仓库
阿里云创建私有仓库,查看当前k8s.io命令空间下的镜像,并修改镜像tag,上传到私有仓库内
[root@master-01 ~]# ctr -n k8s.io i list | grep nginx
registry.cn-guangzhou.aliyuncs.com/caijxlinux/nginx:1.15 application/vnd.docker.distribution.manifest.v2+json sha256:e770165fef9e36b990882a4083d8ccf5e29e469a8609bb6b2e3b47d9510e2c8d 42.7 MiB linux/amd64 io.cri-containerd.image=managed
[root@master-01 ~]# ctr -n k8s.io image tag registry.cn-guangzhou.aliyuncs.com/caijxlinux/nginx:1.15.12 registry.cn-guangzhou.aliyuncs.com/caijxlinux/login:1
registry.cn-guangzhou.aliyuncs.com/caijxlinux/login:1
[root@master-01 ~]# ctr -n k8s.io images push --user aliyun7423505462 registry.cn-guangzhou.aliyuncs.com/caijxlinux/login:1
Password: //此处提示输入密码
manifest-sha256:e770165fef9e36b990882a4083d8ccf5e29e469a8609bb6b2e3b47d9510e2c8d: done |++++++++++++++++++++++++++++++++++++++|
config-sha256:53f3fd8007f76bd23bf663ad5f5009c8941f63828ae458cef584b5f85dc0a7bf: done |++++++++++++++++++++++++++++++++++++++|
elapsed: 1.4 s total: 6.8 Ki (4.9 KiB/s)创建deployment控制器,尝试直接拉取镜像创建容器
[root@master-01 ~]# vim /k8spod/config/private-image.yaml
apiVersion: apps/v1
kind: Deployment
metadata:
name: nginx-deployment
labels:
app: nginx
spec:
replicas: 1
selector:
matchLabels:
app: nginx
template:
metadata:
labels:
app: nginx
spec:
containers:
- name: nginx
image: registry.cn-guangzhou.aliyuncs.com/caijxlinux/login:1可以观察到,镜像拉取失败
[root@master-01 ~]# kubectl create -f /k8spod/config/private-image.yaml
deployment.apps/nginx-deployment created
[root@master-01 controllers]# kubectl get pods
NAME READY STATUS RESTARTS AGE
cluster-test-665f554bcc-bcw5v 1/1 Running 172 (15m ago) 61d
nginx-deployment-5c59bb7b87-tnq5q 0/1 ImagePullBackOff 0 50s创建用于拉取个人仓库的secret
[root@master-01 ~]# kubectl create secret docker-registry secret-tiger-docker --docker-username=aliyun7423505462 --docker-password=实际密码 --docker-server=registry.cn-guangzhou.aliyuncs.com
secret/secret-tiger-docker created查看创建的secret类型
[root@master-01 ~]# kubectl get secrets
NAME TYPE DATA AGE
secret-tiger-docker kubernetes.io/dockerconfigjson 1 3m48s修改yaml配置文件
[root@master-01 ~]# vim /k8spod/config/private-image.yaml
apiVersion: apps/v1
kind: Deployment
metadata:
name: nginx-deployment
labels:
app: nginx
spec:
replicas: 1
selector:
matchLabels:
app: nginx
template:
metadata:
labels:
app: nginx
spec:
imagePullSecrets:
- name: secret-tiger-docker
containers:
- name: nginx
image: registry.cn-guangzhou.aliyuncs.com/caijxlinux/login:1重新创建资源,可以观察到镜像已经成功拉取下来
[root@master-01 ~]# kubectl create -f /k8spod/config/private-image.yaml
deployment.apps/nginx-deployment created
[root@master-01 ~]# kubectl get pods
NAME READY STATUS RESTARTS AGE
cluster-test-665f554bcc-bcw5v 1/1 Running 172 (23m ago) 61d
nginx-deployment-56bcdd64b8-rkdhm 1/1 Running 0 5sSecret配置证书
实验环境下通过Openssl创建私有证书
[root@master-01 ~]# openssl req -x509 -nodes -days 365 -newkey rsa:2048 -keyout tls.key -out tls.crt -subj "/CN=test.com"
Generating a 2048 bit RSA private key
.........+++
....................................................................................+++
writing new private key to 'tls.key'
-----通过命令行创建Secret,读者可以在官网查询到yaml方式配置的Secret【https://kubernetes.io/zh-cn/docs/concepts/configuration/secret/#tls-secret】
[root@master-01 ~]# kubectl -n default create secret tls nginx-test-tls --key=tls.key --cert=tls.crt
secret/nginx-test-tls created通过之前已经创建的ingress文件,添加tls字段,并创建资源
[root@master-01 ~]# cat /k8spod/service/ingress-domain-tls.yaml
apiVersion: apps/v1
kind: Deployment
metadata:
name: nginx
labels:
app: nginx
spec:
replicas: 3
selector:
matchLabels:
app: nginx
template:
metadata:
labels:
app: nginx
spec:
containers:
- name: nginx
image: registry.cn-guangzhou.aliyuncs.com/caijxlinux/nginx:v1.15.1
ports:
- containerPort: 80
---
kind: Service
apiVersion: v1
metadata:
name: back-service
spec:
selector:
app: nginx
ports:
- protocol: TCP
port: 80
targetPort: 80
---
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:
name: nginx-ingress
spec:
tls:
- secretName: nginx-test-tls
ingressClassName: nginx
rules:
- host: nginx.test.com
http:
paths:
- backend:
service:
name: back-service
port:
number: 80
path: /
pathType: ImplementationSpecific修改本地的hosts文件或DNS服务器,添加域名和IP的对应关系
192.168.132.169 nginx.test.com查看Ingress映射的端口,通过域名https://nginx.test.com进行访问,此时浏览器提示不信任证书,添加信任即可正常访问
[root@master-01 ~]# kubectl get svc -n ingress-nginx
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
ingress-nginx-controller NodePort 10.96.155.204 <none> 80:31058/TCP,443:31804/TCP 12d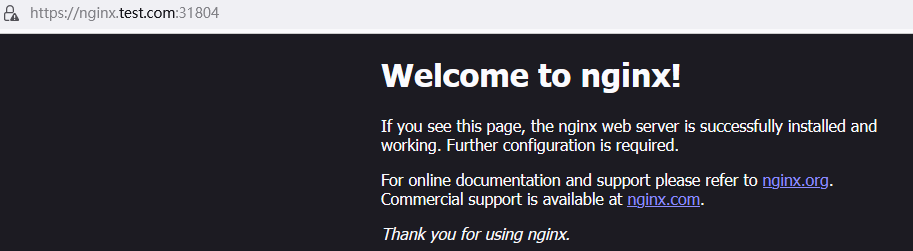
SubPath解决挂载覆盖
在config挂载时,会存在覆盖问题,如果挂载的目录本身下面有文件,直接挂载会将目录下的文件全部覆盖,导致报错,此时可以使用SubPath字段进行控制,只挂载单个文件。
修改nginx.conf配置文件内worker_connections连接数为4096
kubectl exec -it nginx-76649d58b-xjsxd -- cat /etc/nginx/nginx.conf > /nginx.conf】
[root@master-01 ~]# sed -i 's/worker_connections\s\+[0-9]\+/worker_connections 4096/' /nginx.conf
[root@master-01 ~]# cat /nginx.conf | grep worker_connections
worker_connections 4096;通过命令行和nginx.conf配置文件,创建ConfigMap
[root@master-01 ~]# kubectl create cm subpath --from-file=/nginx.conf
configmap/subpath created
[root@master-01 ~]# kubectl describe cm subpath
Name: subpath
Namespace: default
Labels: <none>
Annotations: <none>
Data
====
nginx.conf:
----
\r
user nginx;\r
worker_processes auto;\r
\r
error_log /var/log/nginx/error.log notice;\r
pid /var/run/nginx.pid;\r
\r
\r
events {\r
worker_connections 4096;\r
...省略部分输出...修改configmap配置文件
[root@master-01 ~]# vim /k8spod/config/subpathfielmount.yaml
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
app: dp-cm
name: dp-cm
spec:
replicas: 1
selector:
matchLabels:
app: dp-cm
strategy: {}
template:
metadata:
labels:
app: dp-cm
spec:
volumes:
- name: subpathmount
configMap:
name: subpath
containers:
- image: registry.cn-guangzhou.aliyuncs.com/caijxlinux/nginx:v1.15.1
name: nginx
volumeMounts:
- name: subpathmount
mountPath: /etc/nginx/nginx.conf
subPath: nginx.conf
创建资源,并查看配置文件是否只针对nginx.conf单个覆盖(读者可以尝试不添加subPath字段,nginx.conf会直接覆盖/etc/nginx目录下的全部内容,导致容器启动失败)
[root@master-01 ~]# kubectl create -f /k8spod/config/subpathfielmount.yaml
deployment.apps/dp-cm created
[root@master-01 ~]# kubectl exec -it dp-cm-779bbff6b4-bxkhf -- cat /etc/nginx/nginx.conf | grep worker_conn
worker_connections 4096;ConfigMap热更新
针对于某些配置文件,如果是通过yaml文件生成的,在更新文件之后,使用Kubectl replcae命令更新即可。如果通过conf文件生成的,就无法使用kubectl replcae命令进行更新
先修改nginx.conf文件,worker_connections连接数为512
[root@master-01 ~]# sed -i 's/worker_connections\s\+[0-9]\+/worker_connections 512/' /nginx.conf
[root@master-01 ~]# cat /nginx.conf | grep worker_connections
worker_connections 512;使用--dry-run命令和replcae命令相结合更新配置文件(此时进入容器内,可以观察到nginx.conf的配置文件并没有发生变化,这是因为程序自身并不支持热更新)
[root@master-01 ~]# kubectl create cm subpath --from-file=/nginx.conf --dry-run=client -oyaml | kubectl replace -f -
configmap/subpath replaced只读Secret
只读的Secret有两个好处,第一是防止意外(或非预期的)更新导致应用程序中断,其次(对于大量使用 Secret 的集群而言,至少数万个不同的 Secret 供 Pod 挂载), 通过将 Secret 标记为不可变,可以极大降低 kube-apiserver 的负载,提升集群性能。 kubelet 不需要监视那些被标记为不可更改的 Secret
创建一个Secret,并添加immutable 字段
root@master-01 ~]# kubectl create configmap readonly --from-literal=username=cjx -oyaml --dry-run=client > /k8spod/config/readonly.yaml
[root@master-01 ~]# vim /k8spod/config/readonly.yaml
apiVersion: v1
kind: ConfigMap
metadata:
creationTimestamp: null
name: readonly
data:
username: cjx
immutable: true创建资源,并添加password字段
[root@master-01 ~]# kubectl create -f /k8spod/config/readonly.yaml
configmap/readonly created
[root@master-01 ~]# vim /k8spod/config/readonly.yaml
apiVersion: v1
kind: ConfigMap
metadata:
creationTimestamp: null
name: readonly
data:
username: cjx
password: cjx
immutable: true更新配置文件,提示错误,错误信息为:禁止,字段不可变(同样的,使用kubectl edit命令ConfigMap资源也是无法被修改的)
[root@master-01 ~]# kubectl replace -f /k8spod/config/readonly.yaml
The ConfigMap "readonly" is invalid: data: Forbidden: field is immutable when `immutable` is set
学到了啊谢谢
这个 ctr -n k8s.io i list | grep nginx
registry.cn-guangzhou.aliyuncs.com/caijxlinux/nginx:1.15 查询不到镜像是怎么回事呢?
命名空间可能不对,不加命名空间试试
大佬
kubectl get svc -n ingress-nginx
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
ingress-nginx-controller NodePort 10.96.247.52 80:30172/TCP,443:31148/TCP 2d1h
ingress-nginx-controller-admission ClusterIP 10.96.146.182 443/TCP 2d1h
访问 nginx.test.com:31148【不输入https://】 提示Relay failed to nginx.test.com:30172
使用 https://nginx.test.com:31148直接报错,也没有提示不信任证书什么的,我不知道自己目前是做错了哪一步
这种情况应该是流量没有正常被Ingress转发。检查一下svc的endpoint和ingress的对应关系是否正确。检查证书配置和secret是否正确。
我检查了
endpoints
[root@master-01 ~]# kubectl get endpoints
NAME ENDPOINTS AGE
back-service 172.16.184.49:80,172.16.184.50:80,172.16.184.51:80 + 3 more… 13m
kubernetes 192.168.132.169:6443,192.168.132.170:6443,192.168.132.171:6443 4d4h
my-service 172.16.184.49:80,172.16.184.50:80,172.16.184.51:80 + 3 more… 4d4h
nginx-service 172.16.184.49:80,172.16.184.50:80,172.16.184.51:80 + 3 more… 3d
ingress
[root@master-01 ~]# kubectl get ingress
NAME CLASS HOSTS ADDRESS PORTS AGE
nginx-ingress nginx nginx.zkl.com 192.168.132.173 80, 443 14m
ecret
[root@master-01 ~]# kubectl get secret
NAME TYPE DATA AGE
nginx-test-tls kubernetes.io/tls 2 39m
使用内网是可以访问到的
[root@master-01 ~]# curl -k https://nginx.zkl.com:32538
Welcome to nginx!
html { color-scheme: light dark; }
body { width: 35em; margin: 0 auto;
font-family: Tahoma, Verdana, Arial, sans-serif; }
Welcome to nginx!
If you see this page, the nginx web server is successfully installed and
working. Further configuration is required.
For online documentation and support please refer to
nginx.org.
Commercial support is available at
nginx.com.
Thank you for using nginx.
只是在物理机上的C:\Windows\System32\drivers\etc加入了域名却还是访问不了
应该是域名的问题,如果在内网修改了/etc/hosts文件,并且IP解析正常的话,其实代表了流量可以转发。请检查IP和域名的映射关系并清理浏览器缓存,物理机访问也需要带上端口号
今天试用了一下,发现可以了,我不知道为什么,我中途清理了下物理机浏览器缓存,可能确实是物理机清理下缓存就可以了。
是的,那就可以了